
Typical ransomware behavior usually involves encryption of a user's computer files after they run an executable program, or maybe a Javascript file, in order to lower suspicions. However, a new strain of ransomware goes for the bigger piece of the cake, encrypting an entire hard drive aside from the files themselves.
Called Mamba or HDDCrypt, the malware was initially discovered in the Morphus Labs in Brazil. It was also found in machines in the United States and India. According to Renato Marinho, a researcher at Morphus Labs, the malware is believed to be spread through phishing emails and malicious downloads.
Once it infects a machine, it overwrites the host computer's Master Boot Record (MBR) with its own variant, and from there, it will now be able to encrypt the hard drive.
This would mean that if the computer is opened, the system would not fully load, and it would only display a screen controlled by the Mamba ransomware. It will refuse to boot the PC unless the decryption key is provided, which will set back the user one Bitcoin. It will then use two programs called "dccon.exe." and "mount.exe," which are responsible for encrypting the files on the computer, and all mapped network drives.
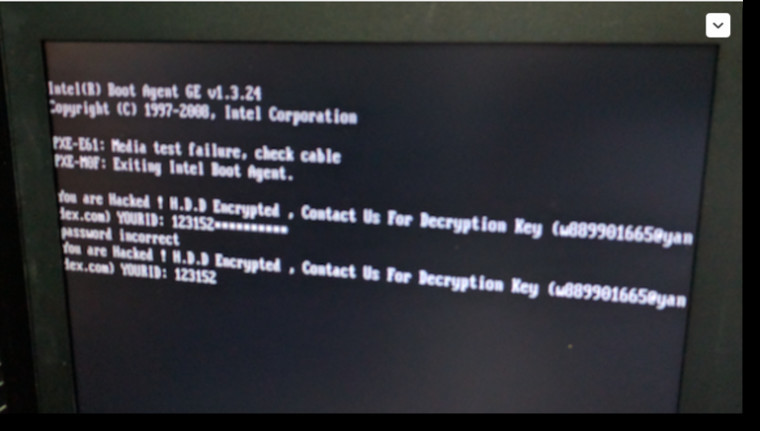
The ransomware note reads:
"You are Hacked ! H.D.D. Encrypted , Contact Us For Decryption Key (w889901665@yandex.com) YOURID: 123152"
“Mamba encrypts the whole partitions of the disk,” according to Marinho. “It uses a disk-level cryptography and not a traditional strategy of other ransomware that encrypts individual files.”
While the Mamba ransomware seems to act a lot like the Petya ransomware, which also manipulates the boot process, the former uses free and legitimate tools. It utilizes Netpass, a free network password recovery tool, as well as DiskCryptor, an open source disk encryption utility.
As per usual, we advise readers to be careful of the websites that they visit and the files that they download, as malware such as Mamba is always waiting in the wings for its next victim.
Source: ThreatPost | HDD Image via Shutterstock

















19 Comments - Add comment