If you're a Python developer and one who is accustomed to installed the latest preview builds of libraries, you might want to take immediate mitigative action. PyTorch, an open-source machine learning framework initially developed by Meta and now under the Linux Foundation, has seemingly been the target of a supply chain attack, which has potentially led to many users installing a malicious package.
Basically, PyTorch-nightly leverages a dependency called "torchtriton". While the library hosted on the PyTorch nightly package index isn't malicious at all, a problematic package with the same name was uploaded to the Python Package Index (PyPI) repository over the holidays.
When Python developers install libraries, they typically utilize the "pip" command in terminal. However, this gives precedence to the PyPI repository, which meant that instead of installing the torchtriton from PyTorch, the malicious binary from PyPI was being installed on user machines.
Fortunately though, the apparent dependency confusion attack has likely not impacted the mainstream Python development community at large. This is because it only affects users of PyTorch-nightly who installed the package on Linux between December 25 and December 30. Users of stable packages are not affected.
Following the discovery of the malicious torchtriton package, the PyTorch development team published a disclosure, and changed the name of the torchtriton package to "pytorch-torchtriton" and registered it as a dummy package on PyPI to prevent similar attacks in the future. Any nightly package using the older name have been removed for now and the team has also reached out to PyPI to get ownership of the "torchtriton" name and delete the malicious version.
An investigation by PyTorch determined that the malicious torchtriton package sent system data from a user's computer to a recent domain, as described below:
-
Get system information
- nameservers from /etc/resolv.conf
- hostname from gethostname()
- current username from getlogin()
- current working directory name from getcwd()
- environment variables
-
Read the following files
- /etc/hosts
- /etc/passwd
- The first 1,000 files in $HOME/*
- $HOME/.gitconfig
- $HOME/.ssh/*
- Upload all of this information, including file contents, via encrypted DNS queries to the domain *.h4ck[.]cfd, using the DNS server wheezy[.]io
In a statement to Bleeping Computer, the owner of the malicious torchtriton package and the domain where user data was being sent defended their actions as being ethical research. They emphasized that:
Hey, I am the one who claimed torchtriton package on PyPi. Note that this was not intended to be malicious!
I understand that I could have done a better job to not send all of the user's data. The reason I sent more metadata is that in the past when investigating dependency confusion issues, in many cases it was not possible to identify the victims by their hostname, username and CWD. That is the reason this time I decided to send more data, but looking back this was wrong decision and I should have been more careful.
I accept the blame for it and apologize. At the same time I want to assure that it was not my intention to steal someone's secrets. I already reported this vulnerability to Facebook on December 29 (almost three days before the announcement) after having verified that the vulnerability is indeed there. I also made numerous reports to other companies who were affected via their HackerOne programs. Had my intents been malicious, I would never have filled any bug bounty reports, and would have just sold the data to the highest bidder.
I once again apologize for causing any disruptions, I assure that all of the data I received has been deleted.
By the way in my bug report to Facebook I already offered to transfer the PyPi package to them, but so far I haven't received any replies from them.
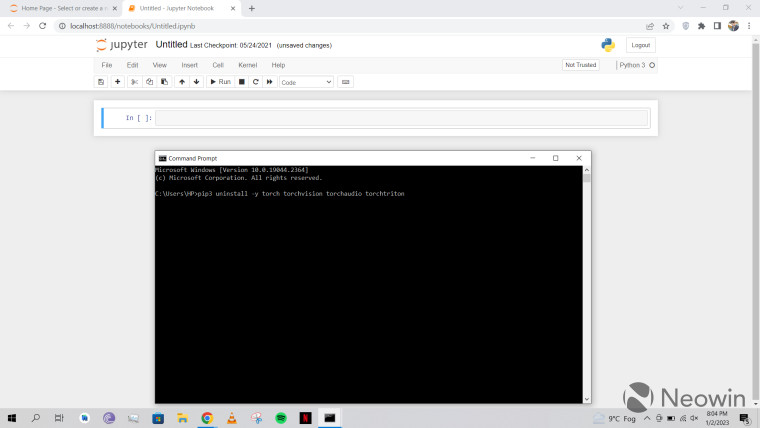
Developers who installed PyTorch Nightly between December 25 and December 30 last year should double-check their systems and run the following commands via pip:
$ pip3 uninstall -y torch torchvision torchaudio torchtriton
$ pip3 cache purge
Similarly, it is also advisable to either switch to PyTorch stable for now or update to a nightly package issued after December 30.
Source: PyTorch via Bleeping Computer





















5 Comments - Add comment