Malware and viruses are nothing new; these nasty pieces of software have been around ever since computers have become popular and a part of every home around the world. There have been countless types and variants already. From ones that wipe a computer's hard drive and alter the BIOS, viruses that promise love, to adware that quietly leaves users vulnerable to hackers and cybercriminals, different methods of committing crimes on the internet is everywhere. However, a new contender has entered the world of malware, and it seems to be wreaking havoc not only to computers, but to people's personal and financial lives as well.

From an innocent-looking email, a user blindly opens a file attached to it, only to find out that they have been had by the bad guys-- and have their computer locked up. Ransomware rose to popularity roughly three years ago through one infamous program-- Cryptolocker. When the malware became rampant, it was easily understood that it was going to be one of the most destructive things out there when it comes to malware to look out for. In just a small amount of time, Cryptolocker can encrypt a computer's files, and then demand money from the innocent victim, with nowhere to run.
So what types of ransomware are there?
Variants of ransomware have spread like wildfire in just a short amount of time. Cryptolocker was quickly followed by TeslaCrypt, which encrypted game files. Cryptowall scrambled a computer's file extensions, aside from encrypting them.
Ransom32, on the other hand, allowed almost anyone to customize their own ransomware. Another variant, called Petya, made it impossible for users to access their computers, as it manipulates the boot process. And lastly, there is even a ransomware now that has the ability to replicate itself through flash drives, making it possible to move from one computer to another.
This list above may just be a small fraction of the number of variants there might be in the wild. Studies by security experts have even shown that the utilization of ransomware by criminals have risen at an alarming pace. Some of what was mentioned above have actually been cracked already, but who knows how many more are out there, patiently waiting in the wings to encrypt people's data and extort money from them?
But wait, what are you exactly trying to say here?
As I mentioned earlier, this kind of malware is unusual compared to the ones we normally encounter, Once infected, the only way to recover is to pay a ransom, which can vary in cost.
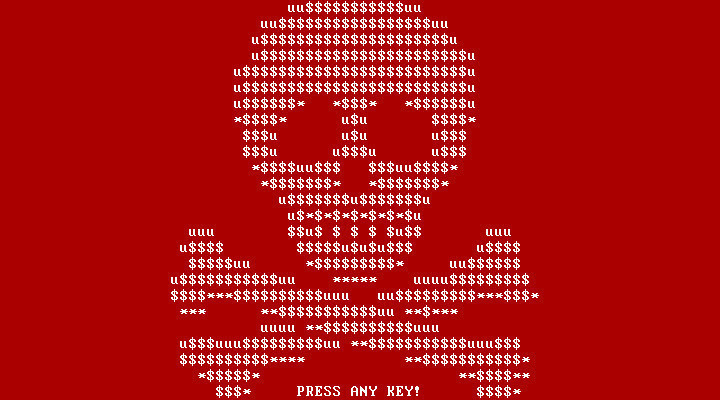
which can be easily terminated by antivirus and anti-malware programs. Once infected, a computer displays a message stating that their files have been encrypted and that the only way to recover them is to pay a ransom, which can vary in cost. You might still be lucky if the ransomware allows you to navigate around the computer, but a lot of ransomware variants lock out users into a single screen, with nowhere to go.
At this point, antivirus software are useless, as your files have already been encrypted. They can have the ability to stop the program, but it would still not help bring the files back, as they can only be freed if the encryption is broken, which antivirus programs cannot do. There have been fixes released, but ultimately, there is no guarantee that they will work for everyone. For one, perpetrators can spew out a new version after new version of their ransomware, dodging the software that can crack their software's encrypting capabilities. Two, there are so many variants out there, which all vary in programming and encryption strength.
What are the consequences of getting infected?
You are usually only left with two choices: pay up and hope that your files will be decrypted, or do nothing, say goodbye forever to your files, and then start over. Let's explore the two options a little bit further. Option 1 is to pay up. With what, specifically? Bitcoins, as the ransomware lock screen says. Well, what the heck is a Bitcoin? Those who have been following tech for a while now may be very familiar with this, a digital payment system where people can directly send money to each other without a mediator. But for those who aren't very literate with computer lingo, one would be instantly confused and thrown off.

Even if people eventually understand what Bitcoin is, the mere fact that it is not easily accessible to people all around the world makes it even more difficult for those who are infected. You cannot just buy it in some convenience store around the corner. Instead, it is a complicated process, by creating Bitcoin People just want their files back and then move on with their lives.
wallets, then locating your Bitcoin address, which is definitely not something a regular computer user would want to go through. Even if we consider that some ransomware demand "money gram cards" that can be bought in physical stores, the process of loading the card onto the computer could still confuse some. Basically, in the end, people just want their files back, and then move on with their lives. Unfortunately, it is still not that easy, as the ransomware even warns the victim that "any attempt to terminate this program would cause permanent destruction of the unique key."
If you pick option 2, it could be a big inconvenience to start over from a clean slate. This is very alarming, even if you say that you don't have personal files in the computer anymore, and just have them in the cloud. Why? For one, it may cost you a lot of money. Way more money than the ransomware might have even asked for. With that in consideration, the cost of having a PC repaired might even be already equal to the cost of buying a new PC. Moreover, not all people who have been infected by ransomware have the capacity to start again from scratch, considering that there are many who are oblivious to what ransomware is in the first place. Lastly, in a corporate setting, getting infected could easily mean that company files will be lost as well. What's worse is that there are some ransomware that can move via connected computers, so that could also mean that one piece of malware could infect an entire network of computers, locking up all the files inside them.
(You can skip over to the section, "What can I do about it?" if you want to know how to stay protected)
There is no assurance how these perpetrators behave. There have been reported instances where individuals and companies paid up, but still did not receive any key or did not have their files decrypted. Taking an incident in Kansas for example, a hospital in the area paid a whopping $20,000 USD, only to realize that they have been had, and will not get their files back. Aside from the large amount of money lost, the institution also lost important documents which help run the hospital's systems. The ransomware creators were even found demanding more money.
With all of these things in consideration, it places a lot of difficulty on the victims on what to do. It leaves not only victims, but everyone else like you who are very likely to contract such malware a lingering question: would it be better to just pay up, and risk the money for the files' recovery, or just ignore everything and start over?
An interview with a tech guy
I had a little talk with long-time Neowinian Adam Bottjen, who you could recognize under the Neowin Forums username warwagon. He currently owns a computer repair business. Throughout his time running it, he has dealt with countless numbers of computer problems already, which recently includes ransomware. I asked Adam a few questions about his experience dealing with CryptoWall, after a customer brought in what seemed to be an encrypted computer."He would talk about a box which was in the middle of his screen talking about how all their files were encrypted and they wanted money."
Asking him how the customer initially described the computer problem, he stated: "He would talk about a box which was in the middle of his screen talking about how all their files were encrypted and they wanted money." Moreover, when asked how they think they got the malware, the customer was reportedly oblivious about it.
Looking into the problem, Adam removed the computer's hard drive and examined its contents via a version of Windows Bootable. The customer's claim was confirmed as he found that the files inside the drive were all locked up.
He then relayed his findings to the customer. The client opted to have the PC reprogrammed instead of just paying up, as he also apparently did not have any backup available to salvage the computer.
Adam emphasizes the importance of backups, specifically disconnected backups when it comes to these types of attacks. He states:
Most people have no backups of any kind to restore from. The small percentage which do would have had a backup connected at the time of infection. You are lucky if anyone has a backup at all, let alone a disconnected backup and almost ZERO have any kind of offsite backup.
His encounter with a customer who had no idea how he got infected with the ransomware clearly shows that it can place so much difficulty on people who just use their PCs for basic purposes, and have no extensive knowledge about how viruses and malware work. Not only they lose access to their files all of a sudden, but they will be burdened further by the idea that they have to decide whether to pay up or do something else to save their computer. In the end, just like his client, people might just opt to have their system reset, and lose their important files forever.
So, what can I do about it?
Ransomware may be rampant, and we can never know when we will get hit by such nasty software in the future. But as they say, prevention is better than cure. Let me highlight a few pointers anyone can take to lower their chances of getting infected by ransomware. These are what could really keep you out of any computer troubles in the future.
-
Always be wary in opening any email. And I mean any email.
This is a big pointer to consider. Phishing is an undeniable favorite pastime of cybercriminals, and it is out there to target the most susceptible of people. These emails might come in a form of job application form, invoice, or something similar.
Via Mailbird
Most of the time, they contain links that appear to lead you to a legitimate-looking website. Usual phishing methods will ask for your login credentials, but it was recently discovered that 93% of phishing emails now contain ransomware. If the sender is not familiar to you, and you do not see the email to be really connected to you, simply delete the email and enjoy the rest of your day. -
Always keep a backup.
As stated earlier, offline backups will work better in these situations. Some variants of ransomware have the ability to delete backup copies on your computer, so the most practical thing to do is to save your files on an external drive. This will not only ensure that no file on your computer goes missing in case something goes wrong, but it will protect your files and memories better. In the end, it's always a good idea to keep your files safe and secure, which will definitely go a long way. -
Always be careful when clicking on ads.
While there are some ads that are safe and help generate revenue for websites, there are some that are just out to steal personal information from users. As much as possible, do not click on internet elements that display messages like "A Media Player update is required to play this content," or "Please install FLV HD to continue." These elements are ads disguised as real messages sent by your computer in order to trick non-suspecting people into downloading their software, which might be loaded with malware. -
Keep your software updated.
Some malware exploit vulnerabilities in programs installed on your computer. Keeping your programs updated could help keep ransomware out of your computer. Keep your antivirus software updated, as well as antimalware, if you happen to be running one. Updating to the latest Windows operating system can be done as well, as Microsoft seems to suggest, but I personally would not necessarily do this. I have been with Windows 7 for many years now, and I have never been infected with one piece of ransomware with my whole time with it. Keeping your core programs updated could already go a long way in battling ransomware.
If you still might be wondering if you'll pay up just in case you get infected, I would personally suggest not to give in. Doing so will only fuel cybercriminals' desires into continuing the business, and infect more people. And as mentioned earlier, you can never know how cybercriminals negotiate, and you can not be assured that they will return all of your files intact and in one piece. Think of it as a life experience, and that we should just learn to be more careful next time on what we do on the internet.
With how much ransomware has grown today, we can never know what might be the next big threat in the future. Hey, it has even invaded the living room. What's next? A refrigerator that refuses to open unless you pay one Bitcoin? Or, as Steven 'Neobond' Parker imagines, maybe a washing machine that holds your beloved clothes and underwear hostage unless you pay up?
Only time (and cybercrooks) can tell.









45 Comments - Add comment