
How often have you been on a conference call and heard someone's clicking keyboard in the background? If you're in a corporation, the answer is probably "daily." At Black Hat, Daniele Lain presented his research on taking those sounds and determining what exactly people are typing. This can be used to steal passwords, email messages, or instant messages without the victim even knowing it's being done.
While research on predicting keys based on typing sound is not new, it previously required placing a microphone near the victim's machine. However, if someone has physical access to your computer, there're easier things the attacker can do to steal information. Everyone uses VoIP solutions and the microphone is already there, eavesdropping on the victim.
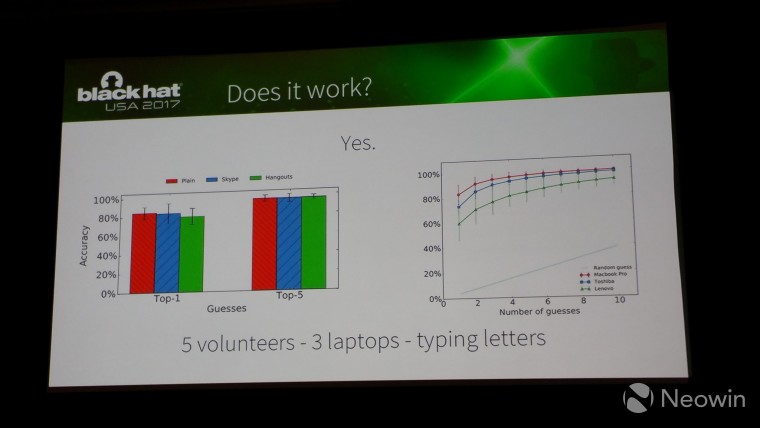
Lain showed data from their research, and what's interesting is that although success rates hover around 80% for the first guess, it's nearly 100% when you make five guesses as to the content of the typing. In addition, the type of keyboard also matters, with the Macbook Pro being the easiest to predict while a Lenovo laptop is currently the most difficult to predict.
If you're interested in trying this out for yourself, the researchers have posted their source code on GitHub. That said, while this attack surface is very real, it also feels like it helps to confirm what Alex Stamos said during the keynote: "It's cool to see someone bypass a hard problem [on stage], but that's not something you'll probably see in the real world."



















3 Comments
Load the comments and join the conversation!
Read the comments, ask the editors questions, show respect and join the conversation.