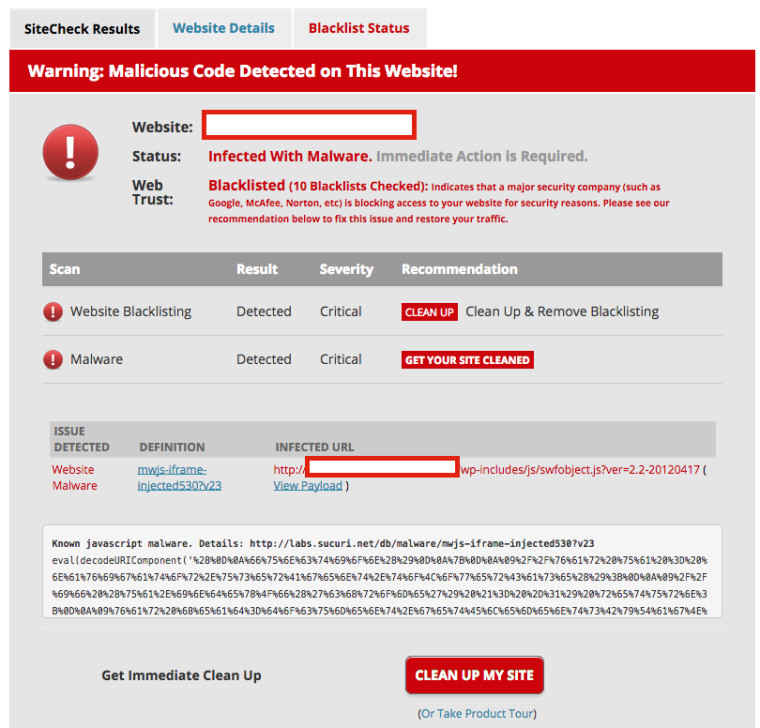
If you are currently running a website under WordPress, now is the time to check your site for infections. According to reports by Sucuri, a server security firm for WordPress, "hundreds of thousands" of WordPress websites have been infected by a malware named SoakSoak, which is capable of turning innocent websites into attack platforms by infecting devices which visit them. As a result, internet browsers could prompt and warn you that a certain website is infected. Google has flagged 11,000 WordPress websites and counting, as of this writing, as malicious.
It has been suspected that a third-party plugin named "Slider Revolution", or “RevSlider” was the culprit behind the attacks; this has been then confirmed by Sucuri. Apparently, according to a statement on the website of the developer, Theme Punch, there was a known vulnerability in the WordPress plugin that was not properly fixed. Instead, they released 29 security patches between February and September, rather than taking proper action in the fears that “an instant public announcement would spark a mass exploitation of the issue”. Reportedly, most users have not updated the plugin, which then led to the attack.
According to Sucuri in its latest post:
“Some website owners don’t even know they have it as it’s been packaged and bundled into their themes. We’re currently remediating thousands of sites and when engaging with our clients many had no idea the plugin was even within their environment,” writes Sucuri on their blog. At this time of writing, WordPress has yet to respond to the attacks.
Sucuri also notes that there will be issues patching the problem as the RevSlider plugin is a premium plugin. They state:
We are hearing a lot of recommendations online to just replace the swfobject.js and template-loader.php files to remove the infection.
It does removes the infection, but does not address the left over backdoors and initial entry points. The website will be reinfected quickly. If you are affected by this, expect to find yourself riddled with backdoors and infections, you have to not only clean, but also stop all malicious attacks. You can stop malicious attacks through the use of a Website Firewall, ours or someone else, just use a Firewall, a real one preferably.
Take note, this attack concerns WordPress.ORG websites, and not WordPress.COM, as the latter does not host plugins.
WordPress has still yet to give a statement on the malware attack.
Source: Sucuri (1) (2), ThemePunch Image: Sucuri









_small.jpg)










19 Comments - Add comment